Halodoc Bug Bounty Program
Halodoc is a health-tech platform aiming to simplify access to healthcare for millions of people around Indonesia. We are committed to protecting our customer data. We also invite researchers outside Halodoc to be able to contribute and participate in reporting security flaws or vulnerabilities through our bug bounty program. Therefore, this blog will share information about the Halodoc Bug Bounty Program and how it complements our existing penetration testing and vulnerability assessment activities.
What is the Bug Bounty Program and Why is it Important?
Bug Bounty is an initiative program that appreciates external security researchers or bug hunters who report vulnerabilities or security flaws in an organisation’s applications / systems / services. For those who are eligible, organisations provide various rewards, such as cash payout, certificates, merchandise, hall of fame, or even offers to become an employee of the organisation. This definitely depends on the program owner within each organisation.
Then, why is Bug Bounty important? Bug bounty programs provide early information about the vulnerabilities or security flaws to the organisation before irresponsible parties or threat actors exploit and abuse them. At the same time, organisations could immediately implement security controls on an ongoing basis.
Bug Bounty Program (BBP) vs Penetration Testing (Pentest)
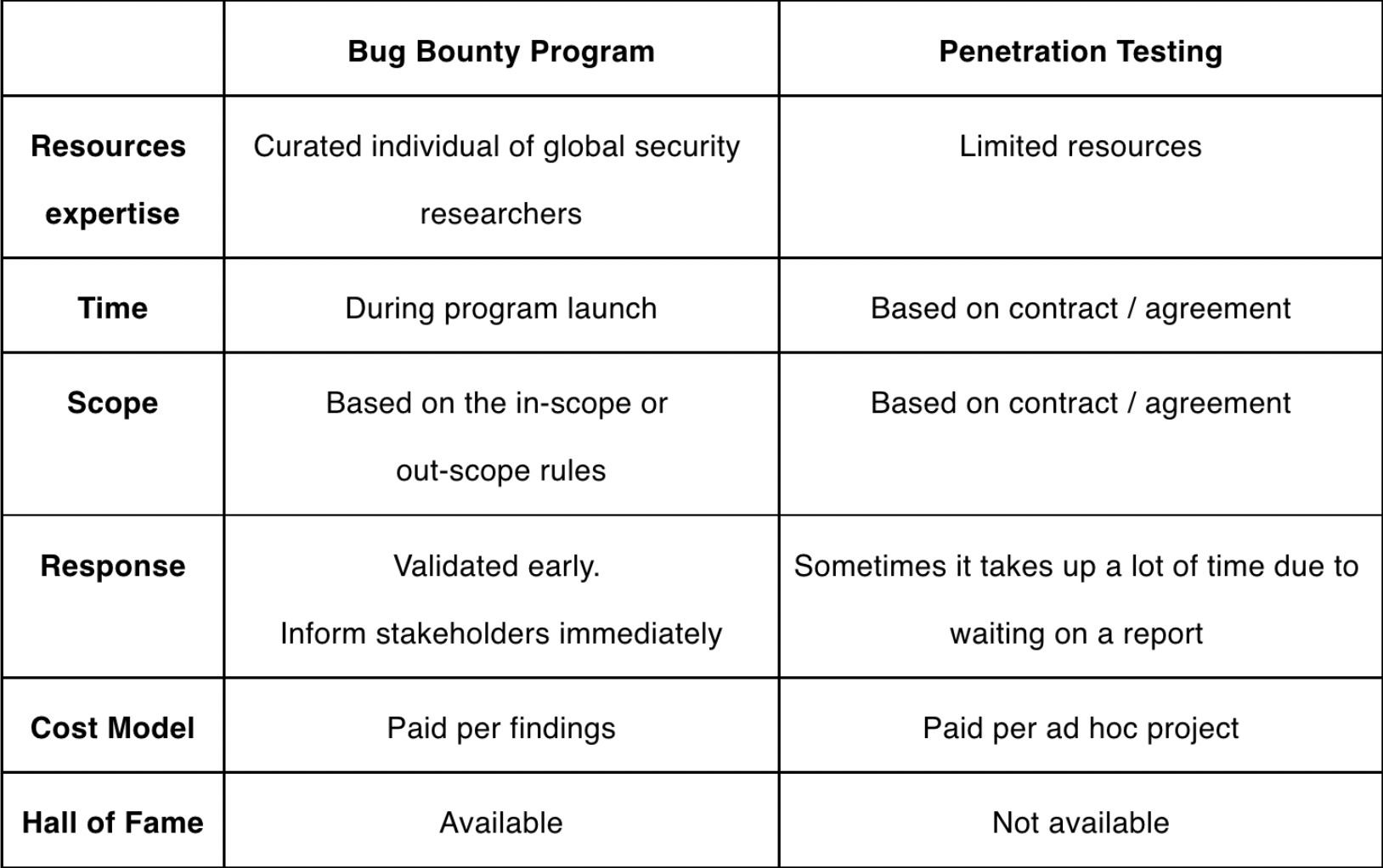
BBP and pentest have similarities in terms of target scope, where both have limitations on the systems that can be tested. But bug bounty programs are not dependent on the specific time frame, while penetration testing is typically conducted for a shorter period of time i.e. one or two weeks. We created the table below for a better summary of the differences.
Halodoc Bug Bounty Program (HBBP)
Halodoc Bug Bounty Program (HBBP) is designed to help Halodoc be more secure to protect customer data. We are aware each vulnerability has a direct and indirect impact. This also designs to reward those who responsibly disclose vulnerabilities on Halodoc properties. We are inviting all security researchers around the world to contribute to our Bug Bounty Program. By participating in this program, it means security researchers follow the responsible disclosure and agree with the terms and conditions that have been published on our website, see the following link https://www.halodoc.com/security.
For the security researchers who reported a valid vulnerability impacting integrity, confidentiality, and availability, and being the first to disclose the vulnerability, they are eligible for rewards or often called bounties.
How Bug Bounty Program Works in Halodoc
Vulnerability Submission
The security researcher could send a vulnerability submission through email to security@halodoc.com. The email must contain at least the following information:
- Vulnerability Name
Security researchers must provide the name of vulnerabilities such as XSS, RCE, etc, in order to provide clarity on the submitted issues. - Vulnerability Description
Security researchers must elaborate the details of the vulnerability into clear and systematic steps, including how to gain unauthorised access or how to exploit the vulnerability. - Proof of concept (logs, screenshots, or video as applicable).
Security researchers must provide the proof of concept as evidence. Without any proof, the Halodoc Security team will not be able to consider the vulnerability. - Vulnerability Impact
Security researchers should elaborate the extent of the impact. For example, if the vulnerability is in the web / mobile application, but there is also an impact on the network and infrastructure, the security researchers must also include detailed elaboration on the network and infrastructure as well. Ticket Management System
Ticket management system
helps Halodoc security team document all vulnerabilities. Halodoc security team will receive vulnerability submission through email. Incoming email will automatically create a ticket into our ticket management system. Attributes and fields will follow based on the email as mentioned in item 1 of Vulnerability Report, as above.
Handling and Response
At the same time, the ticket will trigger an automated alert and notify Halodoc security team. As soon as possible Halodoc security team will validate the vulnerability submission and keep the security researcher informed about the progress. If security researchers find unresponsive feedback, it means that the vulnerability submission is still under review and this needs to involve many relevant stakeholders.
Scoring
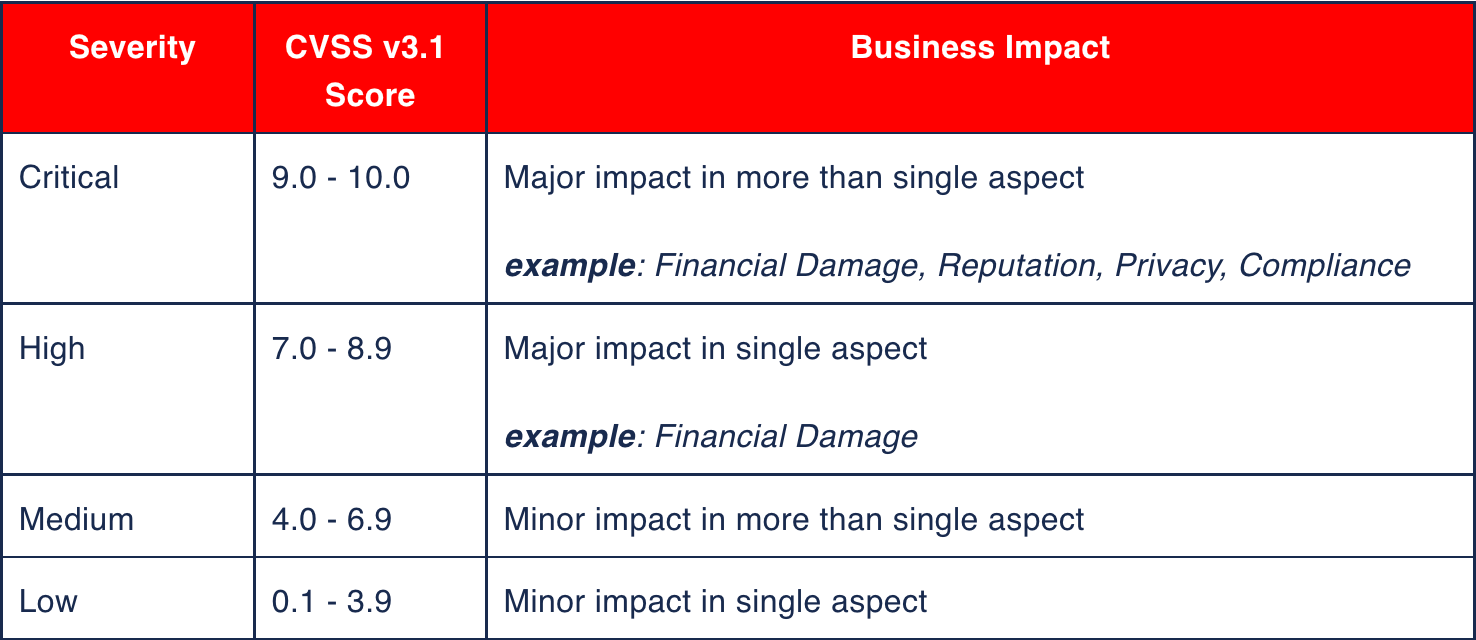
To assess and evaluate the vulnerability submission, we use CVSS v3.1 as a basis. However, it is not the final score as we also consider the impact from the business side such as financial impact, reputation, privacy, compliance, etc. To have a better understanding, please see the applicable matrix that we generally use as below.
Hall of Fame
Security researchers are eligible for appreciation in the form of Hall of Fame at https://www.halodoc.com/security. Security researchers are required to provide detailed information regarding their profile. Then we will post the security researcher's profile on our page.
Conclusion
From what has been written on this blog, we understand that the bug bounty program is also one of the important activities in Halodoc on top of penetration testing and vulnerability assessment activities. With a bug bounty program, Halodoc has additional security advantages, such as gaining vulnerability submission more frequently, improving quality of the vulnerabilities via a curated individual of global security researchers, and continuously enhancing our handling and response as part of cybersecurity incident management. Therefore, Halodoc has invited security researchers to participate in finding security flaws or vulnerabilities in Halodoc environment through Halodoc Bug Bounty Program.
From what has been written on this blog, we know that Halodoc currently has a Bug Bounty Program aimed to all security researchers in the world. In HBBP, they can participate in this program by submitting vulnerability reports. They also are required to follow the rules and applicable laws. Halodoc security team will validate the incoming report as soon as possible. Once the report is valid, then the security researcher has the right to obtain some kind of appreciation, it could be a reward or hall of fame page. Halodoc believes, together with ethical hackers and security researchers we can make Halodoc more secure.
References:
- https://www.halodoc.com/security
- https://idnsa.id/article/program-bug-bounty-berhadiah-dari-halodoc
- https://cyberthreat.id/read/4112/Hai-Hacker-Ayo-Cari-Bug-di-Halodoc-Ada-Hadiahnya
- https://bughunters.google.com/about/rules/6625378258649088/google-and-alphabet-vulnerability-reward-program-vrp-rules
Scalability, reliability and maintainability are the three pillars that govern what we build at Halodoc Tech. We are actively looking for data engineers/architects and if solving hard problems with challenging requirements is your forte, please reach out to us with your resumé at careers.india@halodoc.com.
About Halodoc
Halodoc is the number 1 all-around Healthcare application in Indonesia. Our mission is to simplify and bring quality healthcare across Indonesia, from Sabang to Merauke. We connect 20,000+ doctors with patients in need through our Tele-consultation service. We partner with 1500+ pharmacies in 50 cities to bring medicine to your doorstep. We've also partnered with Indonesia's largest lab provider to provide lab home services, and to top it off we have recently launched a premium appointment service that partners with 500+ hospitals that allows patients to book a doctor appointment inside our application. We are extremely fortunate to be trusted by our investors, such as the Bill & Melinda Gates Foundation, Singtel, UOB Ventures, Allianz, Gojek, and many more. We recently closed our Series B round and In total have raised USD$100million for our mission. Our team work tirelessly to make sure that we create the best healthcare solution personalised for all of our patient's needs, and are continuously on a path to simplify healthcare for Indonesia.




