IT Operations: The Critical Role of Automatic Asset Management
Overview
At Halodoc, constant growth across our Jakarta and Bangalore hubs has rapidly expanded our fleet of devices and systems. What once fit on a single spreadsheet has evolved into a complex infrastructure that demands more than just basic inventory—it requires a robust Endpoint Security foundation.
Maintaining accurate asset status is no longer just an administrative task; it is the frontline of our defense. We realized that manual tracking created a dangerous visibility gap, where any unmonitored device could become a silent entry point for threats. This post outlines how we bridged that gap—moving beyond simply identifying vulnerabilities to automating real-time protection across every endpoint in our network.
The Problem: Visibility Without Control
Effective endpoint security is impossible without full visibility; however, manual procurement workflows often create a dangerous "visibility gap." When hardware is acquired and deployed through administrative channels without integrated IT triggers, devices may enter active use before security baselines are established. These unmanaged assets become silent entry points for unauthorized access because they lack critical endpoint protection from the moment of deployment.
This lack of verified, real-time ownership data cripples Incident Response, as identifying the user behind a flagged device without a linked asset ID can waste hours of manual investigation while a threat spreads. Furthermore, it undermines Vulnerability Management by leaving a subset of the devices exposed to critical CVEs. Ultimately, failing to digitally enforce a continuous chain of custody creates a significant Data Governance Risk, as sensitive corporate information may remain on unrecovered or unconfigured hardware if the lifecycle is not centrally monitored.
What We Built
We designed an automation framework around one core goal: eliminate the gap between detection and action.
- Replaced the manual system with automated asset allocation, thereby establishing a clear, traceable chain from procurement to deployment for every device.
- Enabled real-time alerts for laptop vulnerabilities, which is essential for proactive security risk mitigation.
This systematic, proactive approach is essential for mitigating security risks. It guarantees that all company laptops—including those for new hires and upgrades for current staff—are always fully patched, securely configured, and compliant with company policies. This is vital for significantly reducing the potential for data loss and maintaining the security of our sensitive operational environment.
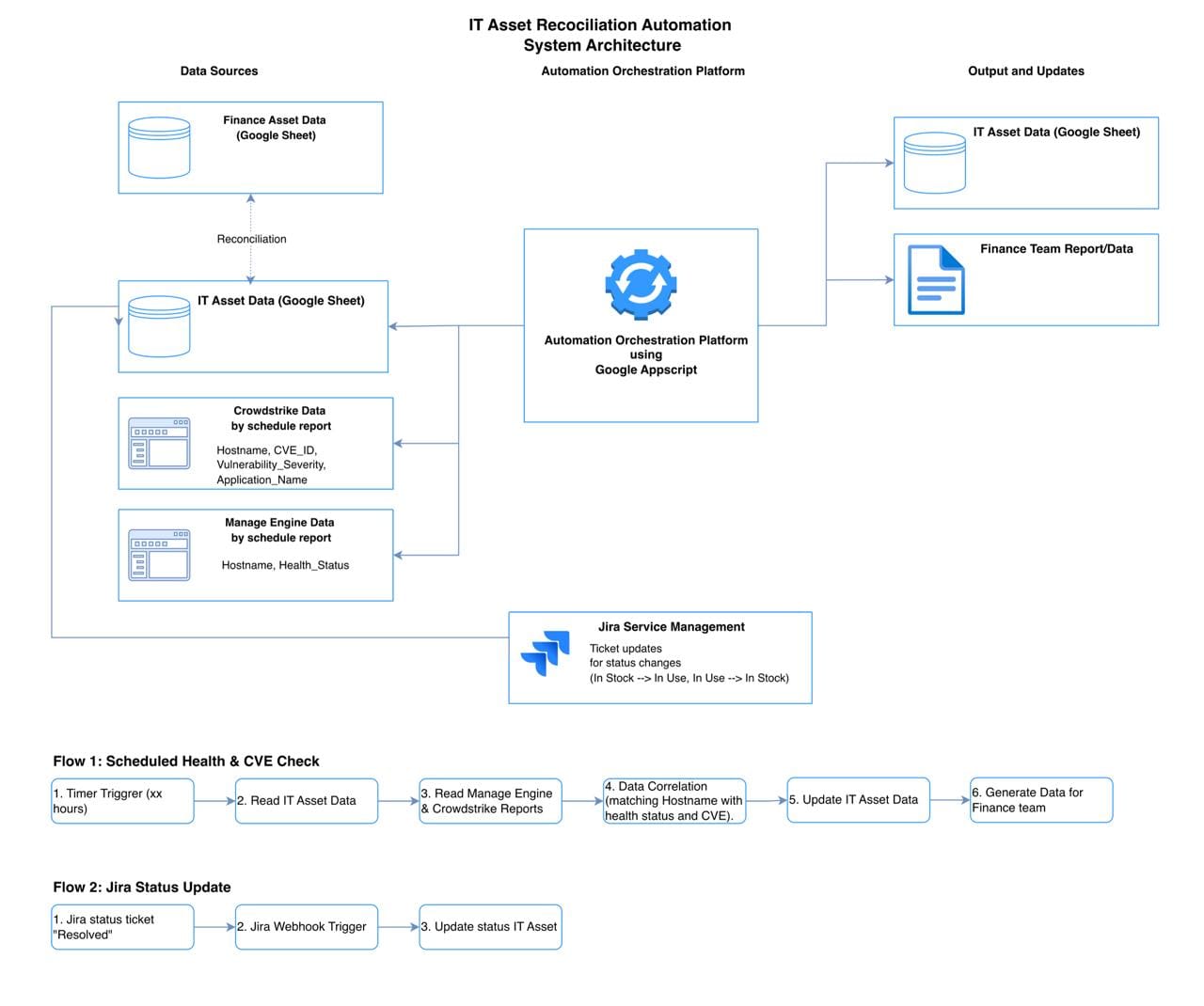
System Workflow Design
The workflow is designed to run in two modes: scheduled (for health data) and event-driven (for status changes).
Flow 1: Asset Health & Vulnerability Check (Scheduled - Daily)
- Scheduled Initiation: The automation platform starts the daily process.
- Active Asset Identification: The system reads the Google Sheet IT Asset Data and retrieves a list of assets with "In-Use" status (e.g., 1000+ assets).
- External Data Collection:
- ManageEngine: The system retrieves the latest System Health Report.
- Crowdstrike: In parallel, the system retrieves Crowdstrike data for each active asset and pulls a list of unhandled CVEs.
- Data Correlation & Processing:
- For each Hostname, the system matches the received data. Example: Hostname ABC123 has a Vulnerable status from ManageEngine and CVE-ID-xxx from Crowdstrike.
- IT Asset Data Update:
- The correlation results (health status, CVE list) are written back to the corresponding rows in the Google Sheet IT Asset Data.
- Finance Team Data Update:
- After all IT data is updated, the system creates a copy of the relevant data (or a summary) and places it in a separate Google Sheet or sends it via email to the Finance team, according to the agreed format.
Flow 2: Asset Status Update via Jira (Event-Driven)
- User Initiation: IT staff creates and resolves a laptop handover ticket in Jira.
- Webhook Trigger: When the ticket moves to "Done" or "Resolved" status, Jira automatically sends a notification (webhook) to the automation platform's endpoint.
- Jira Data Parsing: The automation platform receives data from Jira, extracting key information such as Hostname and new status ("In-Use").
- IT Asset Data Update: The system searches for the corresponding Hostname in the Google Sheet IT Asset Data and changes the value in the Status column from "In-Stock" to "In-Use", and fills in the User column.
Technical Implementation
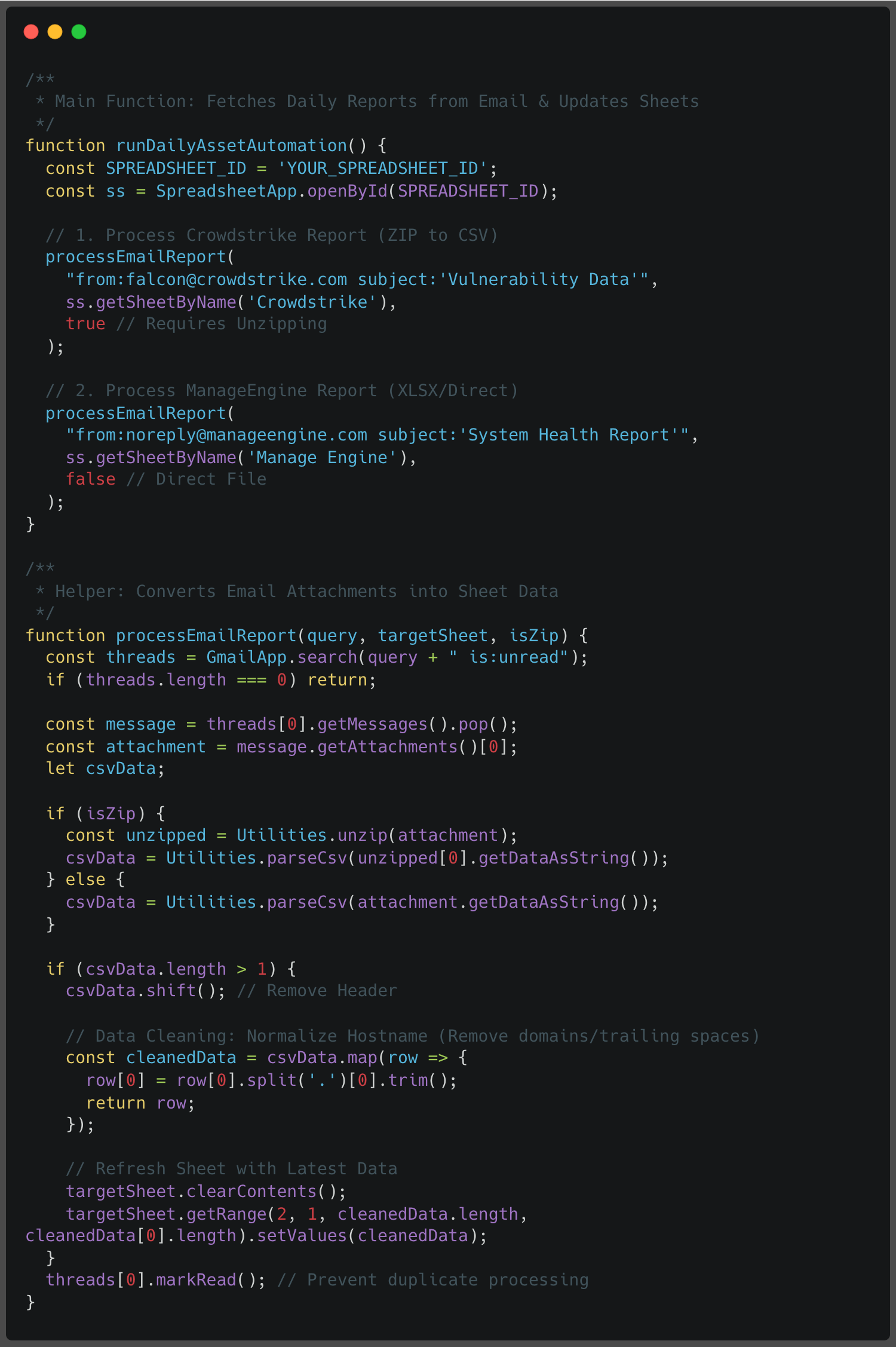
The implementation is structured into a multi-step automated pipeline powered by Google Apps Script.
Step 1: Automated Email Data Extraction
Every morning at 9:00 AM, ManageEngine and Crowdstrike deliver scheduled reports to a designated mailbox. The script identifies these emails, extracts the attachments, and parses the CSV data directly into the IT Asset Data Google Sheet.
Step 2: Data Mapping and Health Determination
Once the raw data is imported, the system performs a lookup against the master IT Asset list. It determines three critical statuses for each asset:
- ManageEngine Status: Is the agent installed and reporting?
- Crowdstrike Status: Is the sensor active on the host?
- Vulnerability Status: Does the asset have unhandled CVEs?
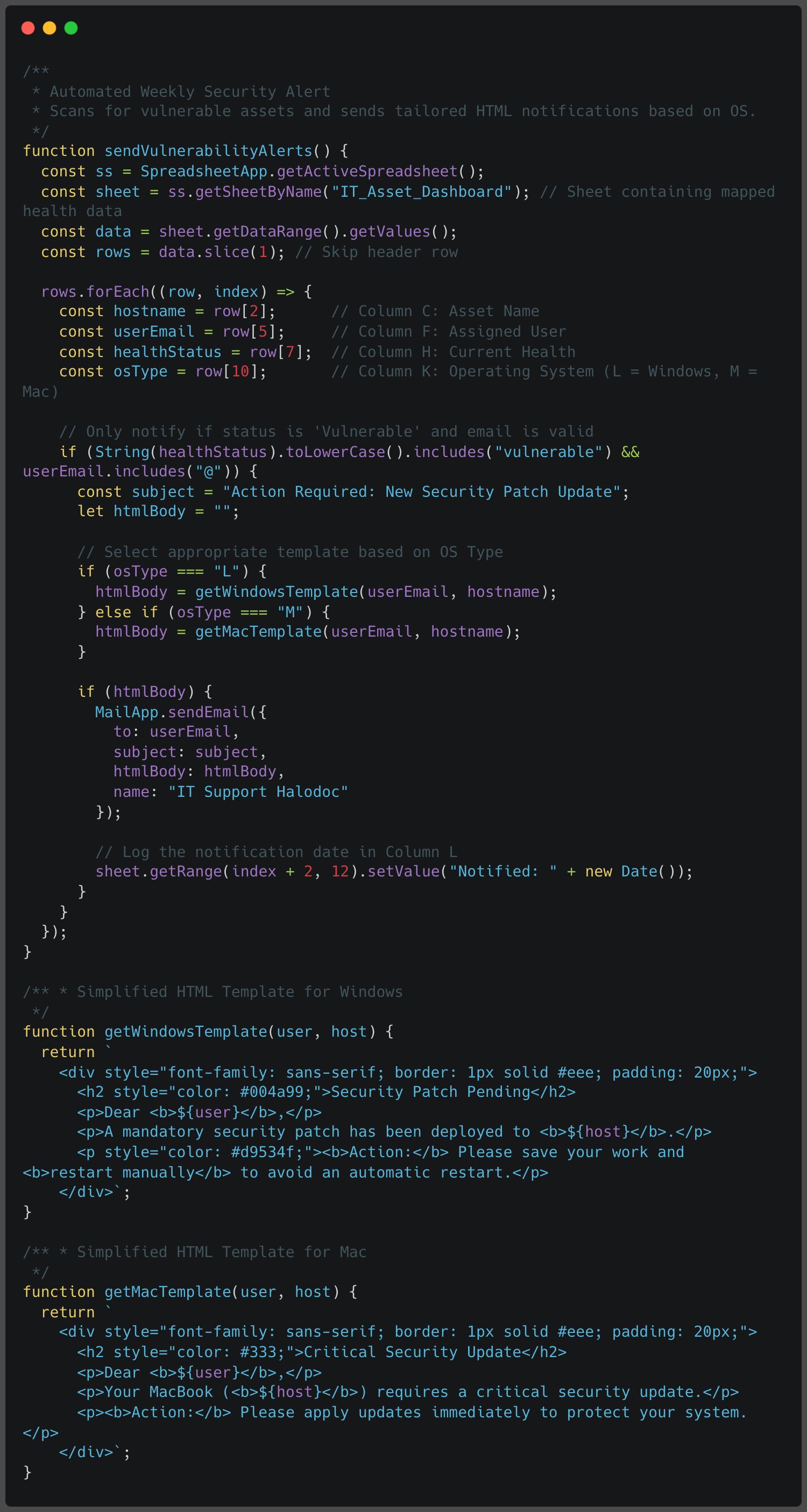
Step 3: Vulnerability Notification Engine
To ensure proactive remediation, the system scans the dashboard every Tuesday for assets flagged as "Vulnerable". It automatically triggers a notification to the responsible party or the IT security team.
Key Metrics and Achievements
This automated approach yields several high-value outcomes:
- Enhanced Data Integrity: Eliminates manual entry errors by relying on unique key identifiers across all systems.
- Installation Visibility: The dashboard clearly identifies gaps where Crowdstrike or ManageEngine agents are missing from laptops.
- Proactive Risk Management: Weekly automated alerts ensure that "Vulnerable" assets are prioritized for remediation.
Where We're Headed
Our goal is clear: every company laptop should always be fully patched, securely configured, and compliant from day one for new hires, and every day after.
That requires a system that doesn't depend on someone remembering to check. It requires automation that treats security as a continuous process, not a periodic event.
The difference between a secure IT environment and a chaotic one comes down to what you can do with your data. Automatic Asset Management turns a spreadsheet of 1000+ rows into actionable, real-time intelligence, for every broken device gets replaced, every vulnerable OS gets patched, every new asset is deployment-ready before it's handed over.
As Halodoc scales, this foundation only becomes more critical. Automation isn't just about saving engineering hours. It's about building infrastructure resilient enough to grow with us.
Automated Asset Allocation
We replaced manual tracking with an automated allocation system that creates a clear, traceable chain for every device — from procurement through deployment to decommission. New joiners now receive assets that are already patched, configured, and policy-compliant before they ever log in.
Real-Time Vulnerability Alerts
Rather than relying on periodic audits, the system surfaces vulnerabilities the moment they're detected and routes specific remediation steps directly to the responsible team. For example:
- CVE-2025-62221 — flagged a required security update for Microsoft Windows 10
- CVE-2025-14174 — triggered an update for Google Chrome Enterprise to version 143.0.7499.109
- CVE-2025-43529 — identified a necessary update for Apple Safari
For every new CVE, the process begins by downloading the patch and applying it to a pilot test laptop. Once the testing phase is successfully completed, the system automatically instructs ManageEngine to deploy the patch remotely to all remaining laptops.
Each CVE is linked directly to its affected Asset ID with a remediation action attached. What would have taken days or weeks to surface manually now happens automatically.
Security Tool Compliance Monitoring
The installation of a security tool does not guarantee its functionality. By continuously monitoring the deployment status of critical agents such as CrowdStrike and ManageEngine, the system utilizes automated flagging to actively verify their operational health.
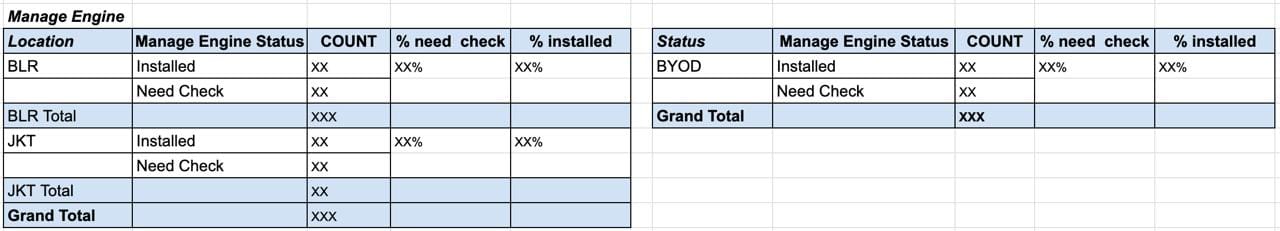
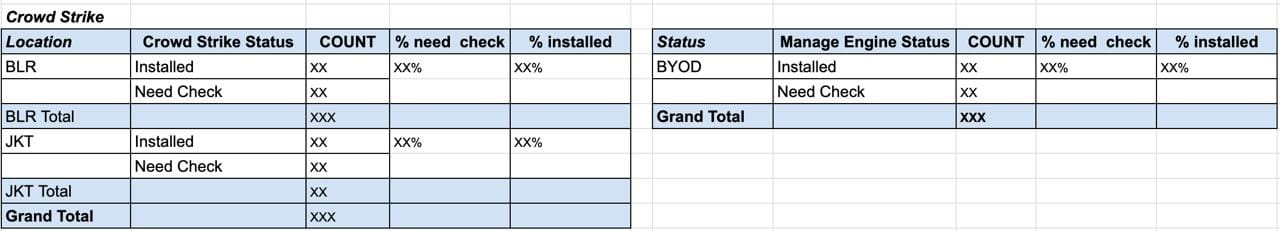
Crowdstrike and Manage Engine.
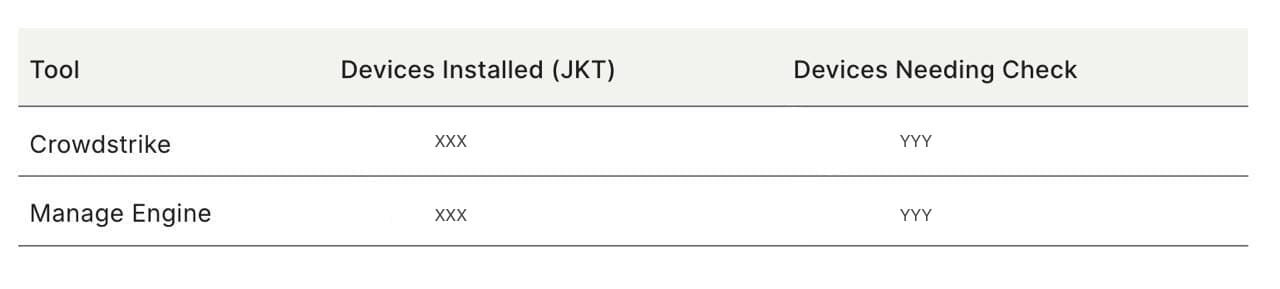
Automatic asset management creates a feedback loop where "Need Check" statuses trigger alerts, ensuring that no device goes efficiently unmanaged or unprotected for long.
Digitized Workflows and Live Dashboards
Manual forms were replaced with digitized workflows that feed directly into a live dashboard. IT support teams receive auto-generated work orders whenever vulnerabilities are detected, keeping response times tight and ensuring nothing falls through the cracks.
Informative and Up to Date
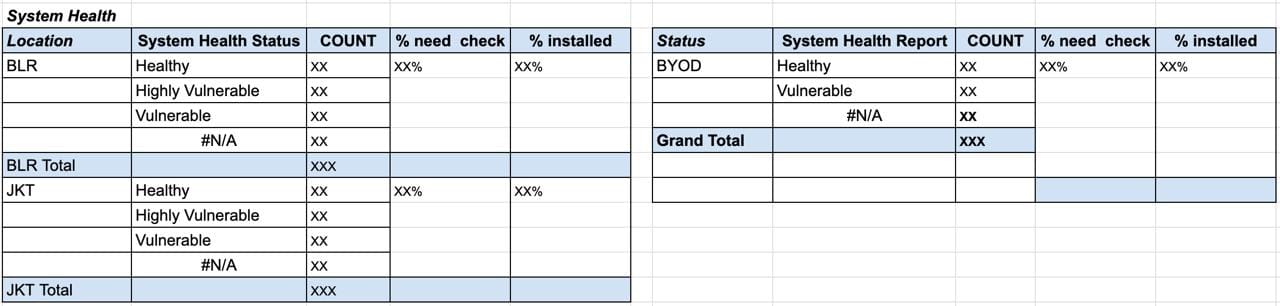
The dashboard offers more than just current status visibility; it also automatically generates work orders for the IT support team. This automation streamlines the process by prompting the team to investigate and update any endpoints where vulnerabilities are detected.
Conclusion
Ultimately, the difference between an efficient IT environment and a chaotic one lies in how to handle the data. By embracing Automated Asset Management, organizations can turn thousand-rows of data into dynamic, actionable intelligence. This guarantees that "Broken" laptops are replaced, "Vulnerable" operating systems are patched, and "In Stock" inventory is always ready to deploy. When a single unpatched device can compromise an entire network, adopting automation is no longer optional but essential.
Join us
Scalability, reliability and maintainability are the three pillars that govern what we build at Halodoc Tech. We are actively looking for engineers at all levels and if solving hard problems with challenging requirements is your forte, please reach out to us with your resumé at careers.india@halodoc.com.
About Halodoc
Halodoc is the number one all-around healthcare application in Indonesia. Our mission is to simplify and deliver quality healthcare across Indonesia, from Sabang to Merauke.
Since 2016, Halodoc has been improving health literacy in Indonesia by providing user-friendly healthcare communication, education, and information (KIE). In parallel, our ecosystem has expanded to offer a range of services that facilitate convenient access to healthcare, starting with Homecare by Halodoc as a preventive care feature that allows users to conduct health tests privately and securely from the comfort of their homes; My Insurance, which allows users to access the benefits of cashless outpatient services in a more seamless way; Chat with Doctor, which allows users to consult with over 20,000 licensed physicians via chat, video or voice call; and Health Store features that allow users to purchase medicines, supplements and various health products from our network of over 4,900 trusted partner pharmacies. To deliver holistic health solutions in a fully digital way, Halodoc offers Digital Clinic services including Haloskin, a trusted dermatology care platform guided by experienced dermatologists.
We are proud to be trusted by global and regional investors, including the Bill & Melinda Gates Foundation, Singtel, UOB Ventures, Allianz, GoJek, Astra, Temasek, and many more. With over USD 100 million raised to date, including our recent Series D, our team is committed to building the best personalized healthcare solutions — and we remain steadfast in our journey to simplify healthcare for all Indonesians.

