Centralized Network Device Authentication using FreeRADIUS
Introduction
Centralized network device authentication plays a critical role in managing efficient and secure access to the network. Currently, Halodoc has implemented FreeRADIUS, a powerful open-source platform with comprehensive capabilities to manage authentication, authorization, and accounting for various network devices such as routers, switches, and firewall. In this blog, we will explore how Halodoc's adoption of FreeRADIUS has successfully improved the efficiency and security of access to our network devices. With the main objective to optimize access to network devices, Halodoc leverages FreeRADIUS as a reliable solution.
What is FreeRADIUS?
FreeRadius is a popular open-source implementation of the RADIUS protocol, which is used for centralized authentication. It is highly customizable and offers a wide range of features, making it an excellent choice for implementing centralized device authentication.
How does FreeRADIUS work?
FreeRADIUS is an open-source, high-performance Remote Authentication Dial-In User Service (RADIUS) server that provides centralized authentication, authorization, and accounting (AAA) services for network devices. Here is a simplified explanation of how FreeRadius functions:
- RADIUS Protocol: FreeRADIUS implements the RADIUS protocol, which is a client-server protocol that facilitates communication between network devices (RADIUS clients) and the RADIUS server.
- Client-Server Communication: RADIUS clients (e.g., network access servers, Wi-Fi access points) send authentication requests to the RADIUS server, typically over UDP (User Datagram Protocol). These requests include user credentials and other relevant information.
- Authentication: The RADIUS server receives the authentication request and verifies the user's credentials against its user database or another designated authentication source (e.g., LDAP, Active Directory). If the credentials are valid, the server sends back an acknowledgment (Access-Accept) to the client.
- Authorization: Upon successful authentication, the server can also send authorization attributes specifying the user's permissions and policies (e.g., access to certain network resources). These attributes help control the user's access rights.
- Accounting: FreeRADIUS can log accounting information, such as user login/logout times, data usage, and other relevant data. This data is essential for auditing, billing, and network management purposes.
Advantages and Challenges of FreeRADIUS
Implementing FreeRADIUS for centralized network device authentication brings several its own set of advantages and disadvantages:
Advantages:
- Open-source: FreeRADIUS is an open-source solution. This makes it a cost-effective choice for organizations of all sizes.
- Customizability: Being open-source allows for extensive customization and adaptation to suit specific network and authentication requirements. Users can modify the code to add features or integrate with multi brand network devices.
- Scalability: FreeRADIUS is known for its scalability, being able to handle a large number of authentication requests efficiently. Can be used in a wide network.
Challenges:
- Limited user interface: FreeRADIUS primarily relies on configuration files, which might be challenging for users who are accustomed to graphical user interfaces (GUIs). While there are some third-party tools that provide GUIs, the core system itself lacks a native one.
- Maintenance: As with any open-source software, ongoing maintenance and updates are necessary to ensure security and compatibility.
Steps of Implementing FreeRadius
The steps undertaken the FreeRADIUS implementation include:
- Install Apache Web Server and PHP
Daloradius will require php and Apache web server to be installed on the host system.Install Apache web server & PHP by running:

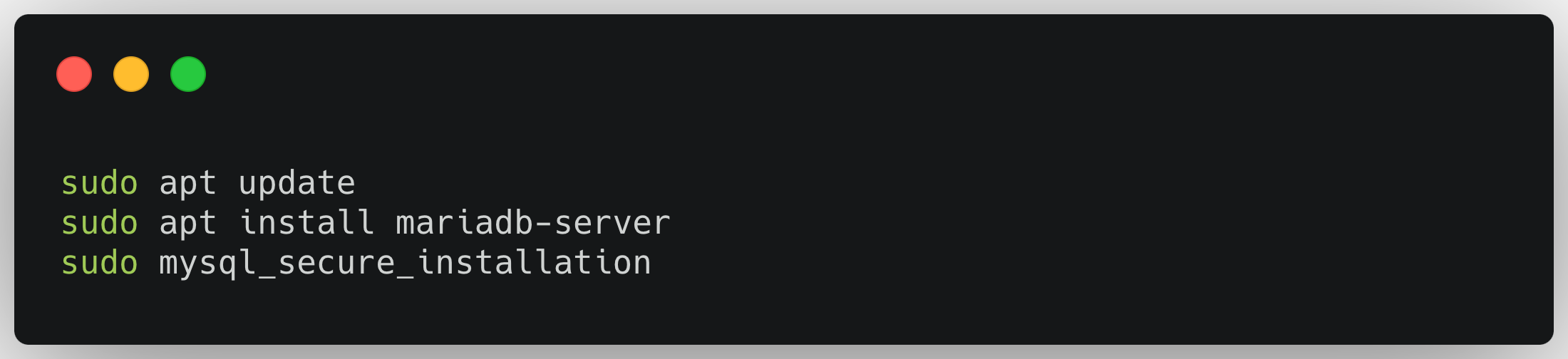
- Install MariaDB and Create a database
Next is to install the MariaDB server and create a database for daloRADIUS:
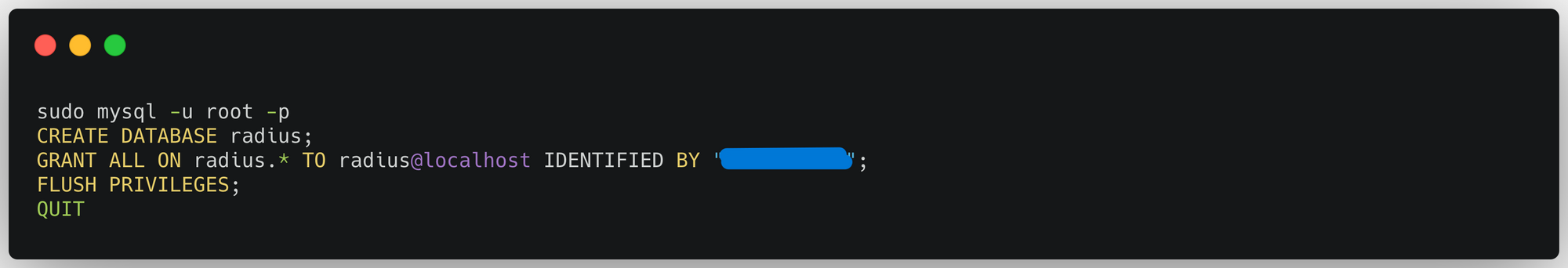
Once installed and running, create a database for FreeRADIUS
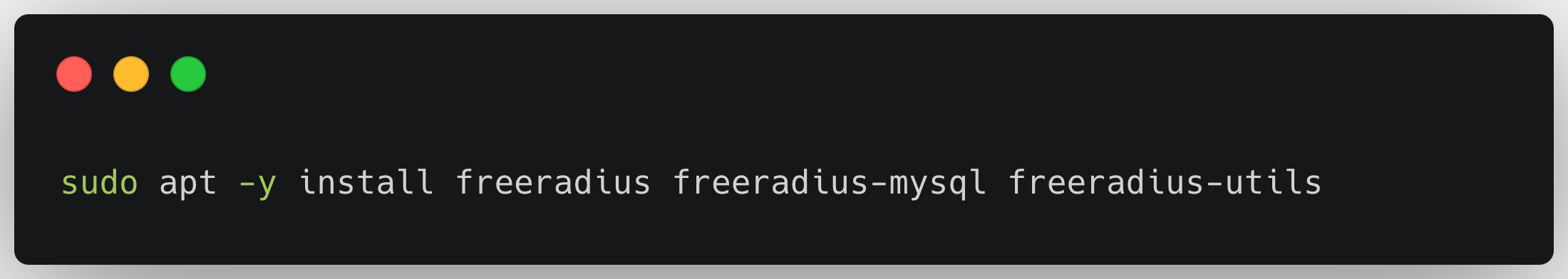
- Install and Configure FreeRADIUS
Install FreeRadius packages with the commands below:
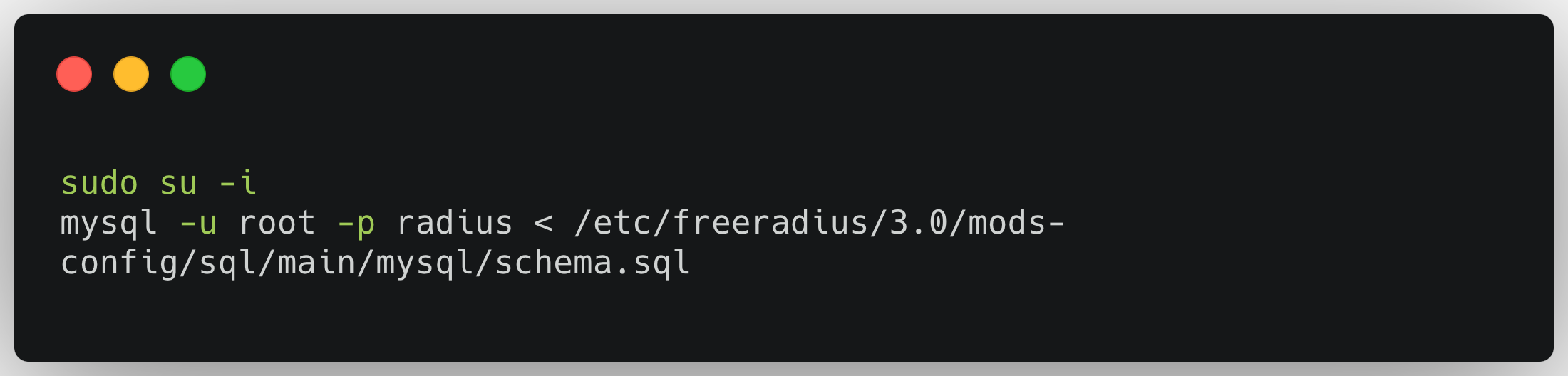
Import the freeradius MySQL database scheme:
Create a soft link for sql module under /etc/freeradius/3.0/mods-enabled/

- Install and Configure daloRADIUS
Install daloRADIUS to get FreeRADIUS web administration interface.

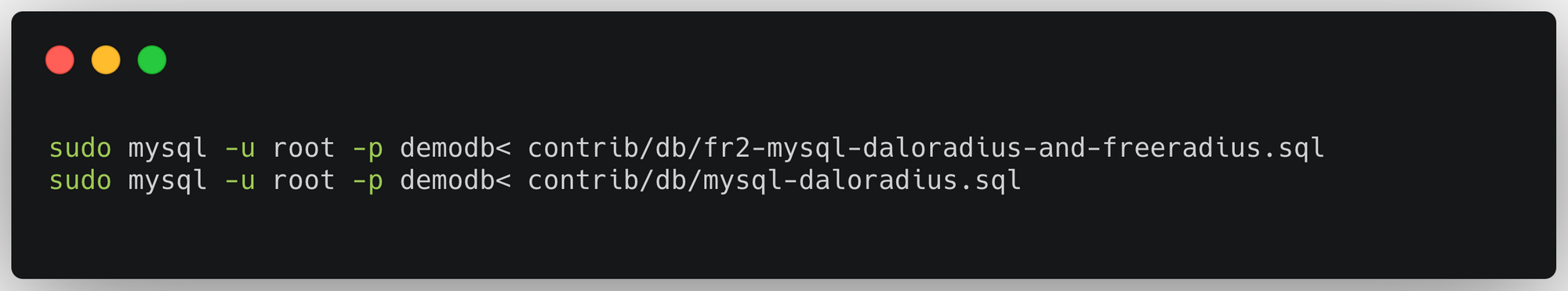
Populate the database with the daloRADIUS schema:
Change the permissions for the daloRADIUS configuration file:

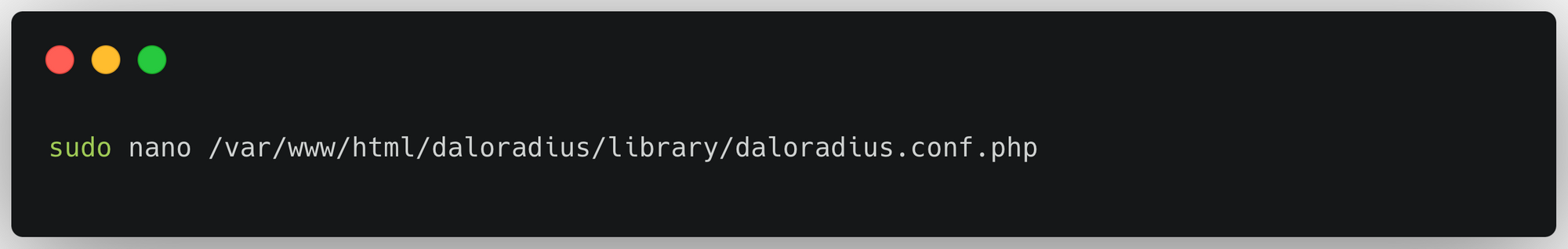
Open the configuration file using your favorite editor:
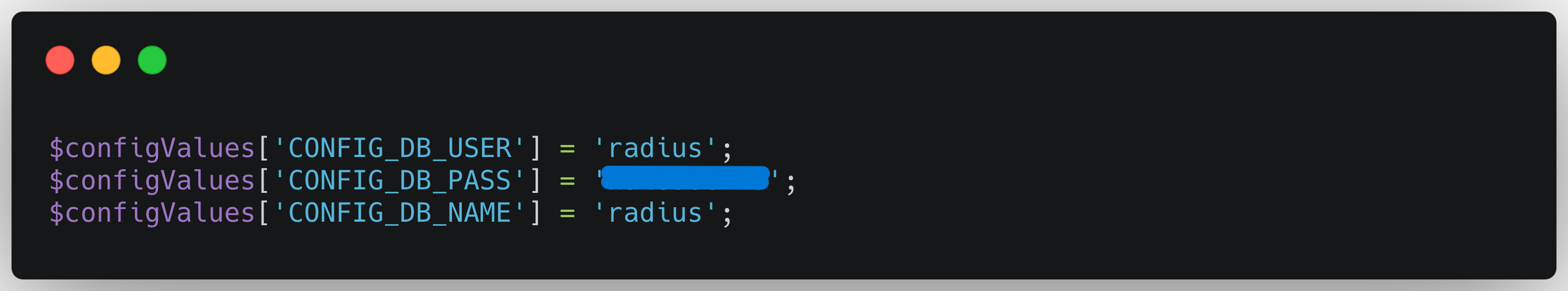
Edit with the details for the database when created earlier:
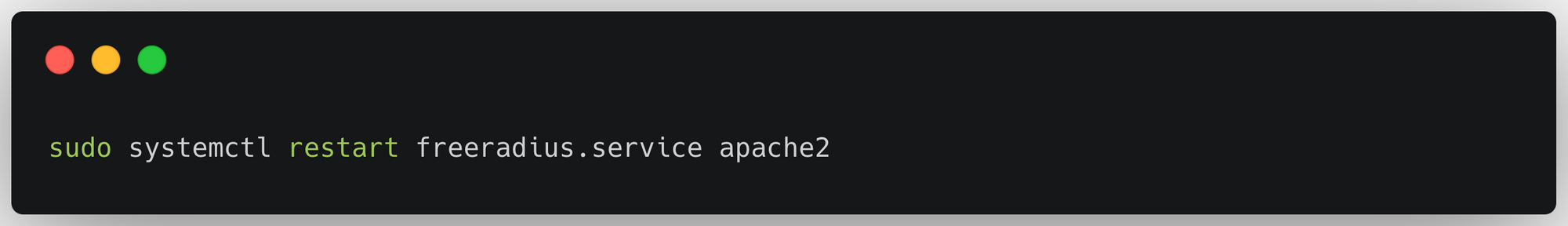
Restart freeradius and apache2:
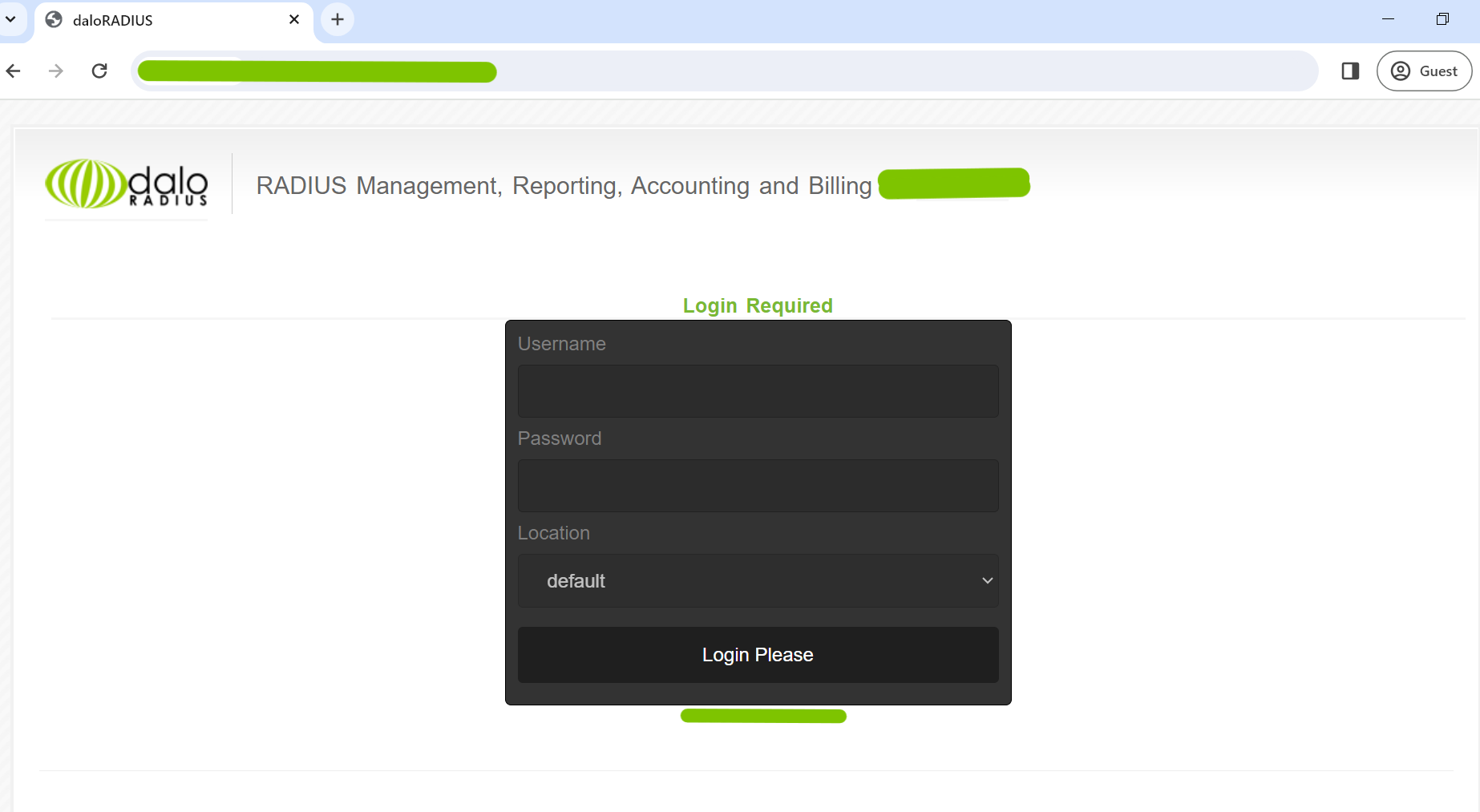
A page like this will appear:
- Create a User Entry
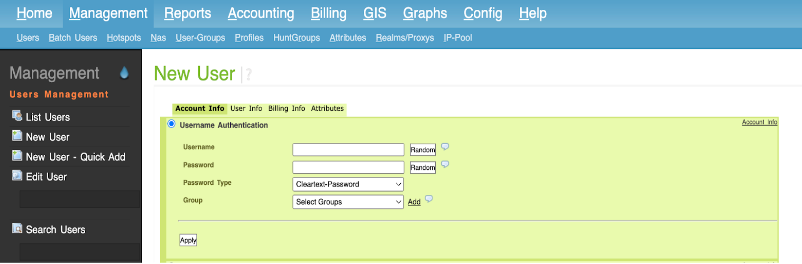
Go to Management > Users, Click on New User
Fill in the required information for the user:
Username: Enter the username of the login network device user.
Password: Enter the user's password.
Group: Select the appropriate user group have defined groups in daloRADIUS.
- Create a NAS Entry
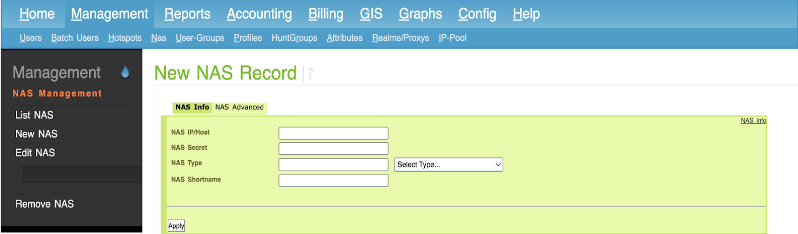
Go to Management > Nas, Click on New NAS
Fill in the required information:
NAS Name: Give your NAS a descriptive name (e.g., "MikroTik Router").
NAS IP Address: Enter the IP address of your Network Devices.
NAS Type: Select the appropriate NAS type, which is usually "other" in this case.
Shared Secret: Enter the shared secret that will be used for communication between the Network Device and the RADIUS server. Make sure it matches the secret configured on the Network Devices.
- Seamless Integration Network Devices: Configure the network device to direct authentication to the RADIUS server:
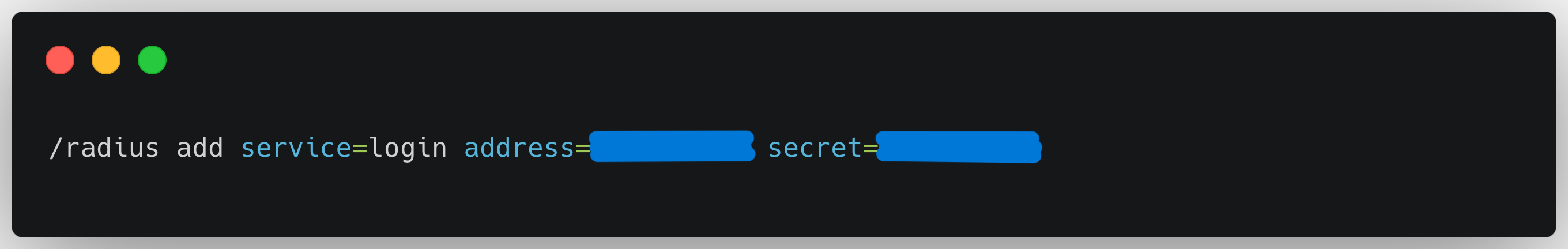
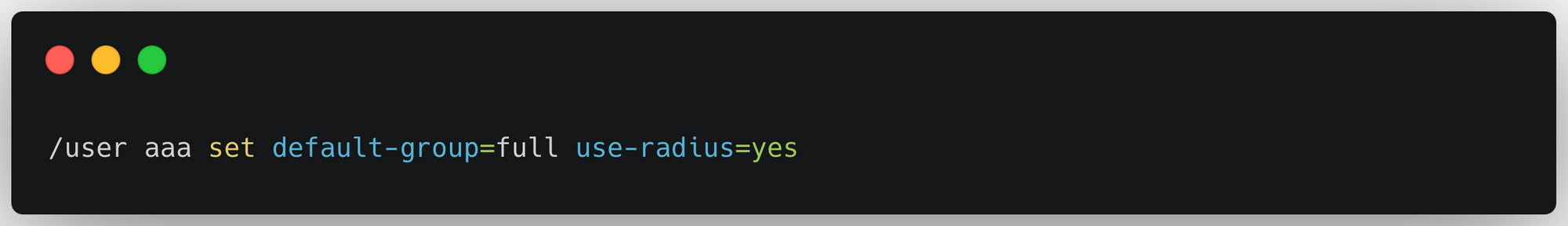
- Configure RADIUS Client in Mikrotik
In MikroTik, set up the RADIUS client configuration to communicate with your FreeRADIUS server. Go to RADIUS and add a new RADIUS server entry.
Set the Service to Login
Enter the IP address of your FreeRADIUS server.
Set the Secret to match the shared secret configured in your FreeRADIUS server.
To enable RADIUS authentication for various services on your MikroTik router, set RADIUS as the authentication method in each service's configuration. Set the Use RADIUS option to "Yes."
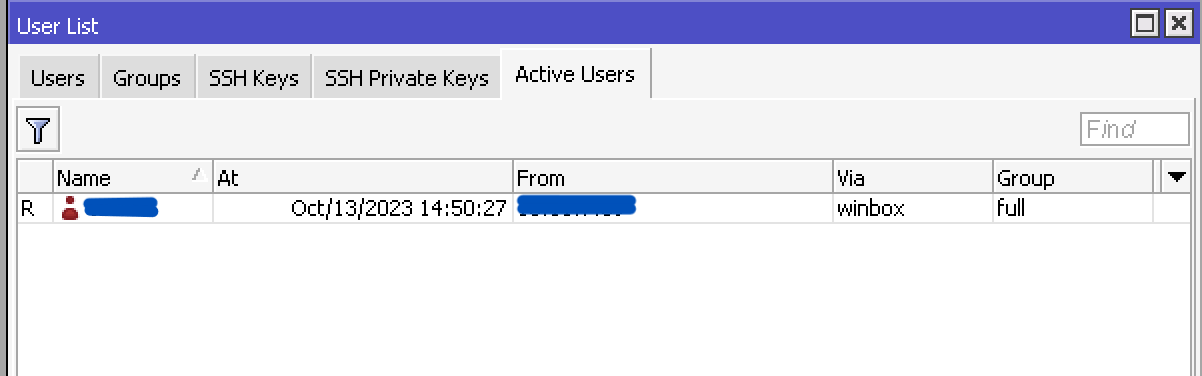
Try logging in with a user account through the MikroTik router login page. the R sign indicates it is a radius authentication
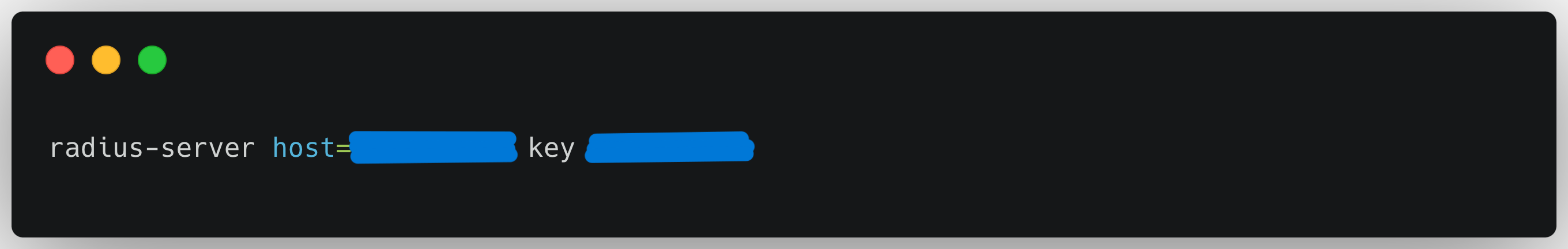
- Configure RADIUS Client in Switch:
In Switch, set up the RADIUS client configuration to communicate with your FreeRADIUS server. Access to Switch with CLI command and add a new RADIUS server entry.
Set the Service to Login
Enter the IP address of your FreeRADIUS server.
Set the Secret to match the shared secret configured in your FreeRADIUS server.
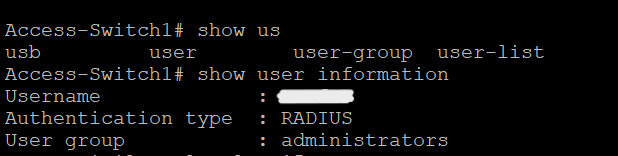
Try logging in with a user account through the Switch login page. The authentication type is RADIUS.
Error Handling
Working with FreeRADIUS, It is important to handle errors properly. There are several steps you can take to troubleshoot issues and resolve them:
- Verify User Authentication and Authorization: Double check the user authentication and authorization configuration in FreeRADIUS. Make sure all the required parameters are set correctly to collect the desired data.
- Logging, Debugging and Monitoring: Configure and monitor the FreeRADIUS logs to record various types of events and errors. Pay attention to log levels, such as debug, info, warning, and error, to filter and identify issues. And also, Set up monitoring systems to alert administrators in real-time when critical errors or failures occur. This helps in immediate response and resolution.
- Regular Testing and Community Involvement: Regularly test your FreeRADIUS server's error-handling capabilities, and keep the server and related software up to date to patch security vulnerabilities. If troubleshooting becomes challenging, reach out to the FreeRADIUS community or support forums for assistance and insights from experienced users.
By following these steps, you can effectively handle errors in FreeRADIUS, ensuring the reliability and effectiveness of your monitoring system.
Benefit Using FreeRADIUS
- High Security: FreeRADIUS is a powerful open-source authentication and authorization solution. Utilizing it helps ensure a high level of security when network devices require access to our network, safeguarding it against unauthorized access.
- Granular Authorization: FreeRADIUS allows us to configure highly detailed authorization rules. we can control device access rights based on specific users or devices, enabling to tailor access to our needs.
- Centralized Management: With FreeRADIUS, we can centrally manage all authentication and authorization policies. This simplifies device and user management across our entire network.
Conclusion
FreeRADIUS is a powerful and flexible tool for enhancing network security and performance. Its comprehensive feature set and extensive customization options make it suitable for a wide range of use cases, from small businesses to large service providers. By leveraging FreeRADIUS, Its can improve the network security posture, optimize network performance, and reduce operational costs.
References
https://networkradius.com/packages/#fr32-ubuntu-jammy
About Halodoc
Halodoc is the number 1 Healthcare application in Indonesia. Our mission is to simplify and bring quality healthcare across Indonesia, from Sabang to Merauke. We connect 20,000+ doctors with patients in need through our Tele-consultation service. We partner with 3500+ pharmacies in 100+ cities to bring medicine to your doorstep. We've also partnered with Indonesia's largest lab provider to provide lab home services, and to top it off we have recently launched a premium appointment service that partners with 500+ hospitals that allow patients to book a doctor appointment inside our application. We are extremely fortunate to be trusted by our investors, such as the Bill & Melinda Gates Foundation, Singtel, UOB Ventures, Allianz, GoJek, Astra, Temasek, and many more. We recently closed our Series D round and in total have raised around USD$100+ million for our mission. Our team works tirelessly to make sure that we create the best healthcare solution personalized for all of our patient's needs, and are continuously on a path to simplify healthcare for Indonesia.




