Solving the iOS developer certificate management hassle with Fastlane
At Halodoc, we constantly work hard to simplify healthcare service across Indonesia. We started with a small team and now we have grown big across all platforms. Right from the beginning we always look for opportunity to automate any routine and time consuming tasks.
Keeping that in mind, we were looking for a way to install development certificates and profiles in a automated way, that will help our team especially new members to setup projects and keep their XCode in sync for code signing in less time.
Introduction to Code signing
Why to Code sign?
- Signing identifies developers to users who downloads their app
- Prevents spoofing (No one else can use the same bundle ID)
How Xcode signs an app?
- It takes the "app bundle" (app executable and any resources used by the app) and applies "Code Seal" to it.
- This allows the system to know about the changes that are made after code signing. So if someone makes any change to the app, system will know it and it won't install & launch the app
3 things required to sign a app
- Signing Certificate - Provided by apple. It is important because device needs a trust chain back to apple so that it can install a app
- Provisioning Profile - It is all about apps, has information such as AppID, Signing Certificate, Capabilities, Devices (In development profile)
- Entitlement - Declares support for Capabilities, It is a string associated with a value for a capability.
Existing approach @ halodoc
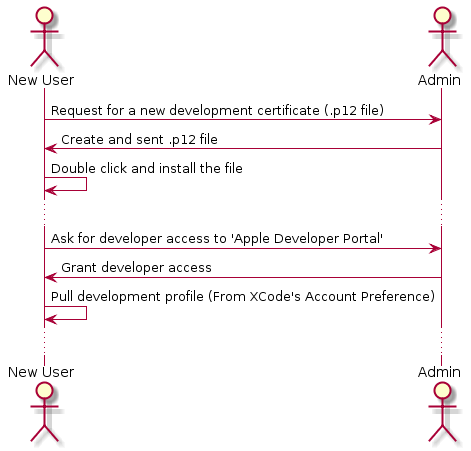
Setting up a new Mac for new team member
- Create CSR from the new Mac and give it to admin
- Admin gives developer access to new member's Apple ID
- Admin creates a development certificate and shares the .p12 file to new member
- New member installs the certificate into Mac by double clicking the .p12 file and downloads profiles from Xcode's "Accounts preference" tab.
- Now they can build and run the project.
Pulling updated certificates and profiles
- Admin updates profile if new UDID has to be included or certificate in case of expired
- Notify all developer to download latest profiles through Xcode "Accounts preference" tab or directly from Developer Portal and provides the new .p12 files in case of certificate updation.
What is the problem with existing approach?
- Each team member have their own certificate. As team grows we will reach the limit of creating development certificates and end up reusing some existing members certificate.
- Dependency on the admin for creating certificates (Though with developer access, anyone can create the certificate from Apple Developer Portal. This dependency will be there if the person isn't familiar with Apple Developer Portal)
- Time consuming - Installing certificates, pulling profiles manually.
What can be improvised in existing approach?
- Admin will create(Or use existing) one development certificate and team members will install the same on their Mac.
- Automate certificates, profiles installation/updation.
Reasons for not using Xcode's "Automatically Manage Sign"?
- Anyone with developer access can Create development profiles , Create and configure AppIDs , Add UDIDs as they wish.
- With 'Automatically Manage Sign' enabled, we can't restrict members(With developer access) from creating/ update certificate, profiles. To put it in simple terms, we can't give read only access to certificates and profiles.
Automation using Fastlane
Introduction to Fastlane
Fastlane is an open source platform aimed at simplifying iOS and Android deployment. It helps in automating every aspect of app development and release workflow such as code signing, distribute beta builds, app store release, screenshots for app store. In here we used to solve the certificate management hassle.
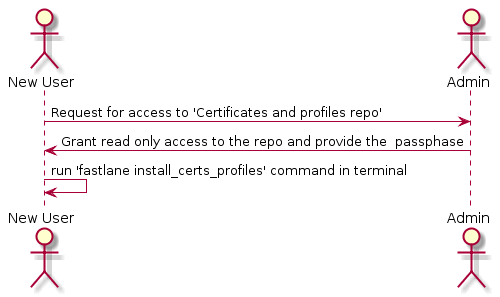
Our ultimate goal for using fastlane is to store one existing development certificate and profiles in a private repo and provide read-only access to team members to pull and install certificates and profiles in their Mac by using simple fastlane commands.
- In order to build and run APP project, one requires read access to certificates and profiles repo and doesn't require access to Apple Developer Portal.
- Installing certificates and profiles in a new Mac can be done in few minutes (Assuming certificates and profile repo read access is granted)
Existing vs Proposed approach:
Responsibilities of the Admin who maintains Certificates and Profiles private repo
Pre-Requisites:
- App Manager access to Apple developer portal
- Read-Write access to Certs and profiles private repo
Responsibilities:
Admin will be updating the repo in following scenarios and notify all members to pull certificate, profiles using fastlane command fastlane install_all_certs_profiles.
- Existing development certificate is revoked and new certificate is created
- Existing profile is modified or a new profile is created to replace existing one.
How to update certificates and profiles repo using fastlane?
- Since we wanted to use existing certificates and profiles rather that letting
fastlanecreate new one. We had to manually manage the repo. - To Manually managing the repo, it's necessary to manually decrypt, then modify, then encrypt the repo, to make any changes. Fastlane's
StorageandEncryptionclasses provides those functionalities
Here is the link for detailed instruction on manually updating the repo.
Security
Being the #1 health care provider of Indonesia with millions of user in our platform, we always keep security as primary goal in whatever we do.
Is storing certificates and profiles in GIT secure?
Both keys and provisioning profiles are encrypted using OpenSSL & passphrase and then stored in a private repo
What could happen if someone stole certificates and profiles?
If attackers would have the certificate and provisioning profile, they could code sign an application with the same bundle identifier.
What's the worst that could happen?
In general, those profiles are harmless as they can only be used to install a signed application on a small subset of devices. To add new devices, the attacker would also need the Apple Developer Portal credentials (which are not stored in Git, but in local keychain).
To sum up
- We have full control over the access list of the private Git repo, no third-party service involved.
- Even if the certificates are leaked, it can only be used to install and run the project on registered devices
Conclusion
We wanted to automated the process of managing Certificate and Profiles in an easier and quicker way so we made use of fastlane.
We were also caution to not provide any kind of write access to our Apple Developer Portal to a third party library like fastlane and that is the reason why we decided to manually maintain our existing certificate and profiles in a private repo.
We are always looking out to hire for all roles for our tech team. If challenging problems that drive big impact enthral you, do reach out to us at careers.india@halodoc.com
About Halodoc
Halodoc is the number 1 all around Healthcare application in Indonesia. Our mission is to simplify and bring quality healthcare across Indonesia, from Sabang to Merauke. We connect 20,000+ doctors with patients in need through our Tele-consultation service. We partner with 1500+ pharmacies in 50 cities to bring medicine to your doorstep. We've also partnered with Indonesia's largest lab provider to provide lab home services, and to top it off we have recently launched a premium appointment service that partners with 500+ hospitals that allow patients to book a doctor appointment inside our application. We are extremely fortunate to be trusted by our investors, such as the Bill & Melinda Gates Foundation, Singtel, UOB Ventures, Allianz, Gojek and many more. We recently closed our Series B round and In total have raised USD$100million for our mission. Our team works tirelessly to make sure that we create the best healthcare solution personalised for all of our patient's needs, and are continuously on a path to simplify healthcare for Indonesia.




