Google Workspace Single Sign-On
Halodoc is a fast-growing Health-Tech company and needs a collaboration tool that can make it easier for every user to collaborate on content creation anytime and anywhere. collaboration tools must also be able to guarantee the security of every user on Halodoc. Halodoc chose Google Workspace Single Sign-On (SSO) as a tool to carry out all collaborative activities because it has high-security standards that can cover the needs of Halodoc users.
Halodoc implemented SSO to secure their data and resources. Secure access to information and technology resources on demand. At the same time, Halodoc must be careful to maintain security controls that prevent unauthorized users from gaining access, as well as blocking legitimate users from exceeding their authorization.
What is Single Sign-On:
SSO or single sign-on, is a access control technology that allows users to log in with a single pair of credentials to several different but related systems or From any device, no matter where they are. An SSO service runs with the help of an authentication token.
Single sign-on process
Google Workspace supports Security Assertion Markup Language (SAML) 2.0 for single sign-on. SAML is an open standard for exchanging authentication and authorization data between a SAML IdP and SAML service providers. we use Google Workspace, external IdP is the SAML IdP and Google is the SAML service provider.
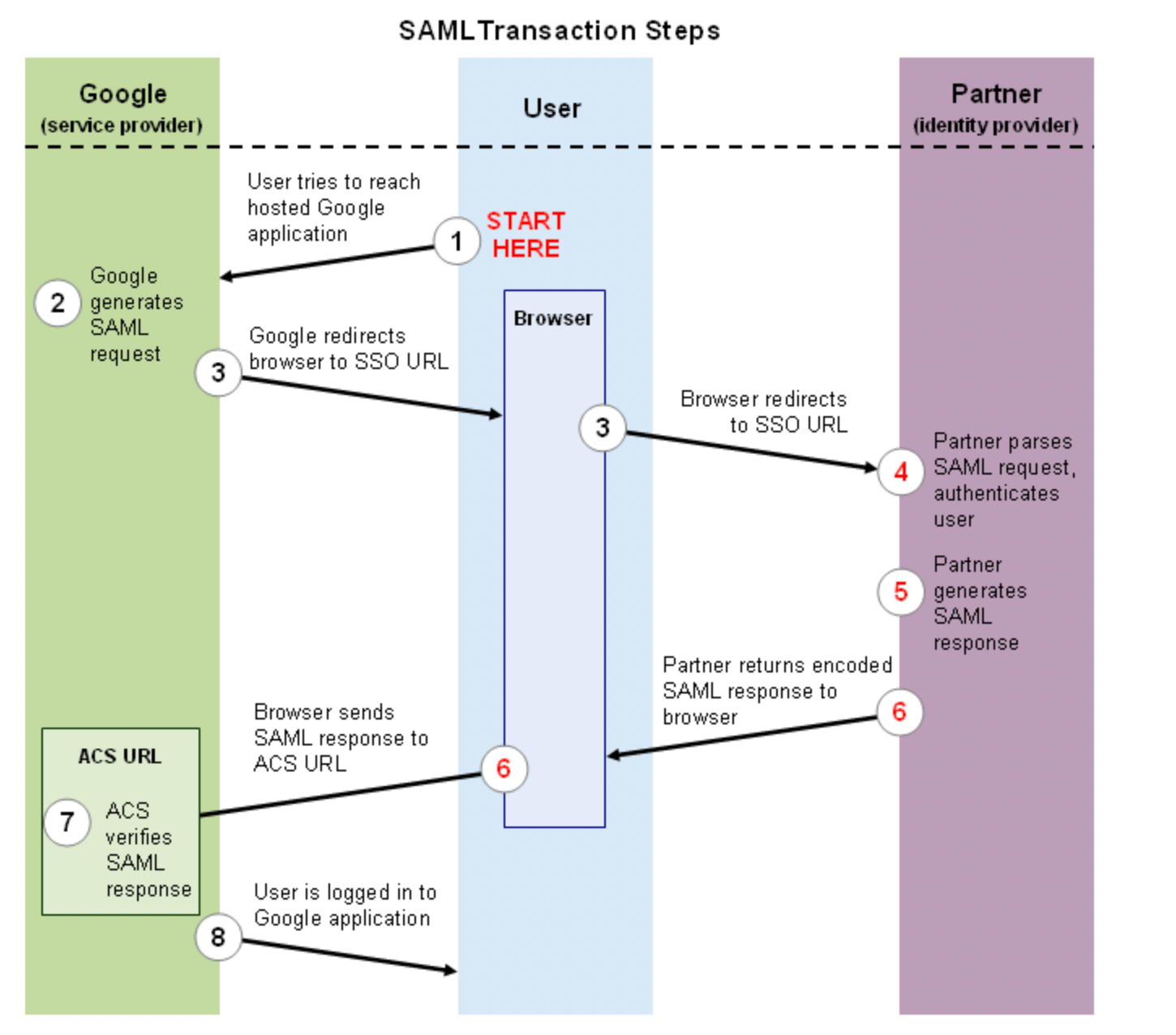
- The user attempts to reach a hosted Google application, such as Gmail, Start Pages, or another Application service that supports SAML.
- Google generates a SAML authentication request. The SAML request is encoded and embedded into the URL for the partner's SSO service. The RelayState parameter containing the encoded URL of the Google application that the user is trying to reach is also embedded in the SSO URL. This RelayState parameter is meant to be an opaque identifier that is passed back without any modification or inspection.
- Google sends a redirect to the user's browser. The redirect URL includes the encoded SAML authentication request that should be submitted to the partner's SSO service.
- The partner decodes the SAML request and extracts the URL for both Google's ACS (Assertion Consumer Service) and the user's destination URL (RelayState parameter). The partner then authenticates the user. Partners could authenticate users by either asking for valid login credentials or by checking for valid session cookies.
- The partner generates a SAML response that contains the authenticated user's username. In accordance with the SAML 2.0 specification, this response is digitally signed with the partner's public and private DSA/RSA keys.
- The partner encodes the SAML response and the RelayState parameter and returns that information to the user's browser. The partner provides a mechanism so that the browser can forward that information to Google's ACS. For example, the partner could embed the SAML response and destination URL in a form and provide a button that the user can click to submit the form to Google. The partner could also include JavaScript on the page that automatically submits the form to Google.
- Google's ACS verifies the SAML response using the partner's public key. If the response is successfully verified, ACS redirects the user to the destination URL.
- The user has been redirected to the destination URL and is logged in to Google.
Challenges to providing users secure access
Users demand quick and easy access to systems and information whether they’re located in the office, at home or on the road. Halodoc recognizes the need for this access but realizes they must balance user demands with difficult security requirements. Cybercriminals know that organizations must support remote users and attempt to exploit enterprise identity systems through the use of social engineering attacks that allow them to compromise the credentials of legitimate users and gain access to enterprise systems. In recent years, social engineering has grown into an increasingly common and effective attack vector.
For decades, passwords served as the primary technology for authentication. From email to online banking, passwords secured the applications that both consumers and businesses rely on every day. Unfortunately, today’s cyberattackers have several potent tools at their disposal that can effectively defeat password-based security mechanisms.
Passwords are particularly susceptible to social engineering attacks. Cybercriminals might call an organization’s help desk and attempt to trick a customer service agent into resetting the password on a legitimate user’s account. Social engineering attacks also take to the web via phishing messages that direct users to fake websites designed to look like legitimate corporate sites but instead harvest passwords for malicious use.
Complex passwords are difficult to guess, but they’re also difficult to remember, prompting users to reuse the same complex passwords across a variety of work-related and personal sites. This poses a significant risk to enterprise security because an attacker who compromises one website and steals a password file may be able to reuse those passwords on work-related sites.
These factors all point in the same direction: The password is rapidly declining as an effective security technology.
Key Advantages of Single Sign-On
1. SSO elevates user experience
How many times have we felt frustrated simply because we couldn't remember username and password for a particular application? Twice? Thrice? Countless times?
SSO offers a much-needed reprieve in this regard.
Employees (or any other users) don't have to key in logins repeatedly. They also do not have to wait on password requests to access essential company tools. That leaves them a happy, satisfied, and productive lot with absolutely no reason to sit on their laurels.
2. SSO saves time
Humans are not machines. As much as we would love to remember dozens of login credentials, we are hardwired to forget a few, or in some situations, all of them.
By deploying SSO, users will be able to access the entire suite of company resources from a single "portal" and with just one pair of credentials—not dozens. This one-click access to requisite modules or services delivers clear and lasting time-saving benefits.
3. Single sign-on improves speed where it matters the most
In high-stake industries , SSO can be incredibly useful. Password misappropriation, or compromised access to shared tools or resources can literally mean the difference between life and death.
4. SSO helps with Compliance
It's no secret that organizations must comply with various regulations like SOX, HIPAA, and, more importantly, PCI DSS (Payment Card Industry Data Security Standard).
The latter requires enterprises to allot unique IDs to all employees with device/resource access and ensure appropriate verification for external users.
5. SSO revamps security
Single sign-on and security are intertwined - they are almost inseparable. The whole concept of a "once-only" login is to beef up the security of sensitive, high-level company resources.
Therefore, to some extent, the SSO acts as a central authentication point. That lowers the chances of phishing or malware attacks.
Conclusion
From what is written in this blog, SSO can reduces the number of attack surfaces, Ease of Use, Transparency and Ease of Access. This is the reason why Halodoc implement SSO for Authentication.
References :
https://support.google.com/a/answer/60224?hl=en
https://blog.miniorange.com/what-is-single-sign-on-sso/
About Halodoc
Halodoc is the number 1 all-around Healthcare application in Indonesia. Our mission is to simplify and bring quality healthcare across Indonesia, from Sabang to Merauke.
We connect 20,000+ doctors with patients in need through our Tele-consultation service. We partner with 1500+ pharmacies in 50 cities to bring medicine to your doorstep. We've also partnered with Indonesia's largest lab provider to provide lab home services, and to top it off we have recently launched a premium appointment service that partners with 500+ hospitals that allows patients to book a doctor appointment inside our application.
We are extremely fortunate to be trusted by our investors, such as the Bill & Melinda Gates Foundation, Singtel, UOB Ventures, Allianz, Gojek, and many more. We recently closed our Series B round and In total have raised USD$100million for our mission.
Our team works tirelessly to make sure that we create the best healthcare solution personalized for all of our patient's needs, and are continuously on a path to simplify healthcare for Indonesia.